In today’s digital landscape, managing user access and permissions has become a critical component of organizational security and operational efficiency. User role permission management tools serve as the backbone of modern access control systems, ensuring that the right people have access to the right resources at the right time.
Understanding User Role Permission Management
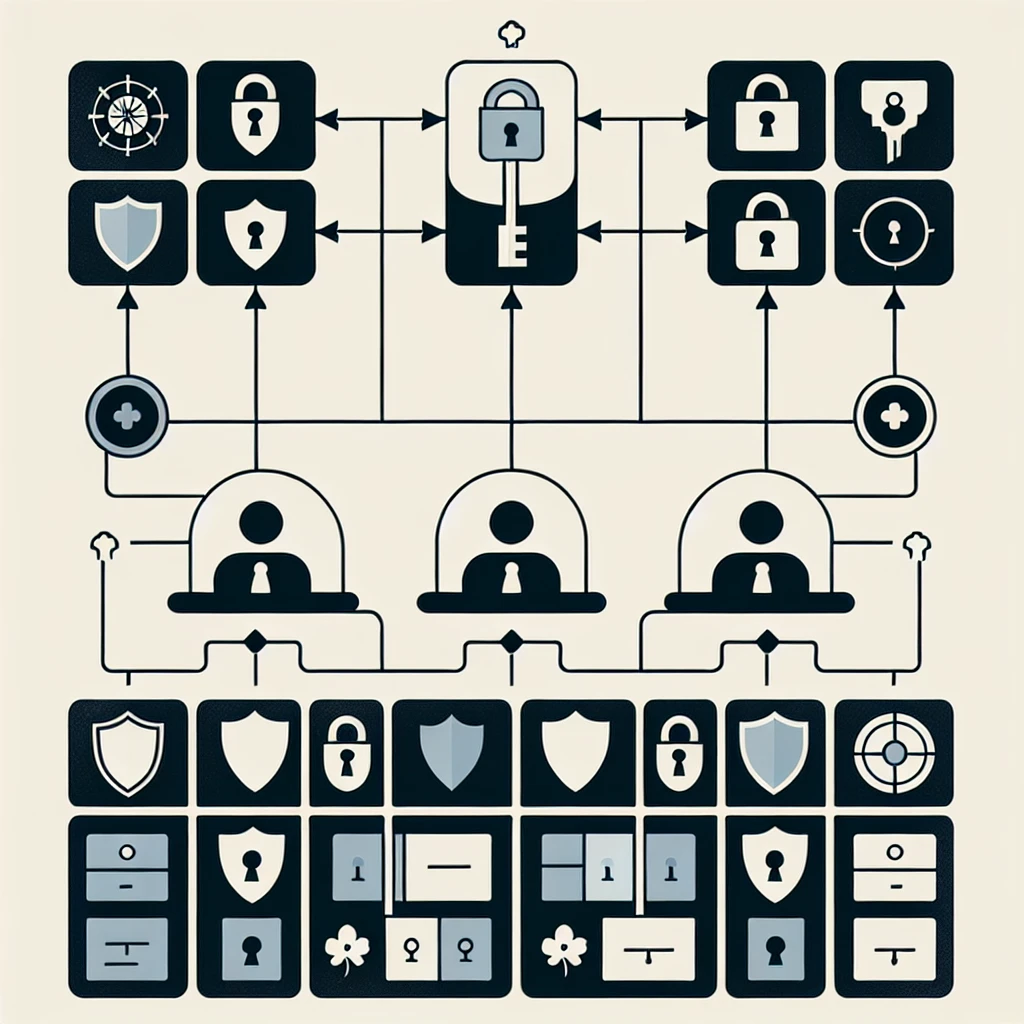
User role permission management represents a systematic approach to controlling access to digital resources within an organization. These tools create a structured framework where permissions are assigned based on predefined roles rather than individual user accounts. This methodology significantly reduces administrative overhead while maintaining robust security standards.
The fundamental principle behind role-based access control (RBAC) lies in grouping users with similar job functions into roles and assigning permissions to these roles collectively. When a new employee joins the organization, administrators simply assign them to the appropriate role, automatically granting all necessary permissions without manual configuration.
Core Components of Permission Management Systems
Role Definition and Hierarchy
Effective permission management tools provide comprehensive role definition capabilities. Organizations can create hierarchical role structures that mirror their organizational chart, ensuring that access levels align with job responsibilities and seniority levels.
- Executive roles with broad system access
- Departmental roles with specific functional permissions
- Project-based roles for temporary access requirements
- Guest roles for external stakeholders
Permission Granularity
Modern tools offer fine-grained permission control, allowing administrators to specify exact actions users can perform on specific resources. This includes read, write, modify, delete, and administrative permissions across various system components.
Dynamic Access Control
Advanced systems incorporate dynamic access control mechanisms that adjust permissions based on contextual factors such as location, time of access, device type, and current security threat levels.
Essential Features of Modern Permission Management Tools
Centralized Administration Dashboard
A comprehensive dashboard provides administrators with a unified view of all user accounts, roles, and permissions across the organization. This centralized approach eliminates the need to manage access across multiple systems individually.
Automated Provisioning and Deprovisioning
Automation capabilities ensure that new users receive appropriate access immediately upon joining, while departing employees have their access revoked instantly. This automation reduces security risks associated with delayed access modifications.
Audit and Compliance Reporting
Robust reporting features generate detailed audit trails showing who accessed what resources and when. These reports prove invaluable for compliance requirements and security investigations.
Single Sign-On Integration
Integration with single sign-on (SSO) solutions provides users with seamless access to multiple applications while maintaining centralized permission control.
Types of User Role Permission Management Tools
Identity and Access Management (IAM) Platforms
Comprehensive IAM solutions offer end-to-end identity lifecycle management, including user provisioning, authentication, authorization, and governance. These platforms typically serve as the central hub for all access-related activities.
Privileged Access Management (PAM) Systems
PAM tools focus specifically on managing and monitoring high-privilege accounts that have administrative access to critical systems. These solutions provide additional security layers for the most sensitive access requirements.
Application-Specific Permission Tools
Many business applications include built-in permission management capabilities designed specifically for their functionality. While these tools offer deep integration with their respective applications, they may lack enterprise-wide visibility.
Cloud-Based Access Management Services
Cloud-native permission management tools provide scalable solutions that grow with organizational needs. These services often include advanced features like machine learning-based access recommendations and automated policy enforcement.
Implementation Best Practices
Principle of Least Privilege
Implementing the principle of least privilege ensures that users receive only the minimum access necessary to perform their job functions. This approach significantly reduces the potential impact of security breaches or insider threats.
Regular Access Reviews
Establishing periodic access review processes helps identify and remove unnecessary permissions that accumulate over time. These reviews should involve both technical administrators and business stakeholders.
Role Mining and Optimization
Analyzing existing user permissions to identify common patterns helps create optimized role structures. This process often reveals opportunities to simplify permission management while improving security.
Segregation of Duties
Implementing segregation of duties prevents any single individual from having complete control over critical business processes. Permission management tools can enforce these controls automatically.
Security Benefits and Risk Mitigation
User role permission management tools provide multiple layers of security benefits that protect organizations from various threats. By implementing centralized access control, organizations can quickly respond to security incidents by modifying or revoking access across all systems simultaneously.
These tools also help prevent privilege creep, where users accumulate unnecessary permissions over time. Regular automated reviews and permission optimization ensure that access levels remain appropriate for current job responsibilities.
Compliance and Regulatory Considerations
Many industries face strict regulatory requirements regarding data access and user permissions. Permission management tools help organizations maintain compliance by providing detailed audit trails, automated policy enforcement, and comprehensive reporting capabilities.
Common regulatory frameworks that benefit from robust permission management include GDPR, HIPAA, SOX, and PCI DSS. These regulations often require organizations to demonstrate who has access to sensitive data and how that access is controlled and monitored.
Integration Challenges and Solutions
Legacy System Integration
Integrating permission management tools with legacy systems often presents technical challenges. Modern tools address these issues through flexible APIs, directory service integration, and custom connector development.
Multi-Cloud Environment Management
Organizations operating across multiple cloud platforms require permission management tools that can provide unified access control across diverse environments. Hybrid solutions offer the flexibility needed for complex multi-cloud deployments.
Application Portfolio Complexity
Large organizations typically maintain extensive application portfolios with varying permission models. Effective tools provide standardized interfaces while accommodating application-specific requirements.
Future Trends in Permission Management
Artificial Intelligence and Machine Learning
AI-powered permission management tools are beginning to offer predictive analytics that can identify potential security risks before they materialize. Machine learning algorithms analyze user behavior patterns to detect anomalous access requests.
Zero Trust Architecture
The shift toward zero trust security models is driving demand for more sophisticated permission management capabilities. These architectures require continuous verification of user identity and access requests regardless of location or previous authentication.
Contextual Access Control
Future permission management tools will incorporate more contextual factors into access decisions, including user behavior analytics, device trust levels, and real-time risk assessments.
Measuring Success and ROI
Organizations implementing user role permission management tools should establish clear metrics to measure success and return on investment. Key performance indicators include reduction in security incidents, decreased administrative overhead, improved compliance audit results, and faster user onboarding times.
Regular assessment of these metrics helps organizations optimize their permission management strategies and demonstrate the value of their security investments to stakeholders.
Conclusion
User role permission management tools represent a fundamental component of modern cybersecurity infrastructure. As organizations continue to adopt cloud services, remote work models, and digital transformation initiatives, the importance of robust access control mechanisms will only increase. By implementing comprehensive permission management solutions, organizations can achieve the optimal balance between security, compliance, and operational efficiency while positioning themselves for future growth and technological evolution.